With the year-end shopping season over, many consumers now have various new smart gadgets in their homes – one particularly popular gadget being smart TVs. These TVs are more than just passive display devices; many of them can even run Android apps as well. While some may find these features useful, these capabilities bring their own risks as well. (This was something that Trend Micro noted two years ago when we first looked at some of the issues of smart TVs.)
Most smart TVs today use older versions of Android, which still contain this flaw. TV brands that sell vulnerable smart TVs include Changhong, Konka, Mi, Philips, Panasonic, and Sharp. In addition, other Android devices with older versions installed are also at risk. Coincidentally, these malicious apps are mainly found in smart TVs or smart TV boxes.
The sites that distribute these malicious apps are located at the following URLs and are under the H.TV name, with most visitors located in the United States or Canada.
Figure 1: Screenshot of sites that serve malware to smart TVs
Figure 2: Screenshot of site that serve malware to smart TVs
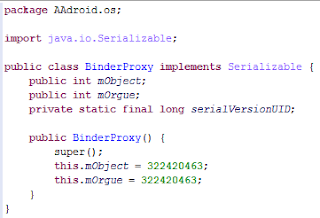
How does the attack happen? First, the attackers lure owners of smart TVs to the websites mentioned above and get them to install the apps infected with malware. Once these are installed, the attacker will trigger the vulnerability in the system. Well-known exploit techniques like heap sprays or return-oriented programming are used to gain elevated privileges in the system.
Figure 3: Malware app triggers the vulnerability
Figure 4: Malware app exploits the system
With elevated permissions, the attacker will then silently install others apps or malware onto the system. Our analysis revealed that they remotely update apps or remotely push related apps to the television sets.
If you’re interested to find out more, follow the link to the blogpost.
For the LATEST tech updates,
FOLLOW us on our Twitter
LIKE us on our FaceBook
SUBSCRIBE to us on our YouTube Channel!