Gemalto Releases Findings of First Half 2015 Breach Level Index
Identity Theft Takes Top Spot Accounting for 53% of Data Breaches
State-Sponsored Attacks See Huge Gains, Accounting for 41% of Stolen Data Records
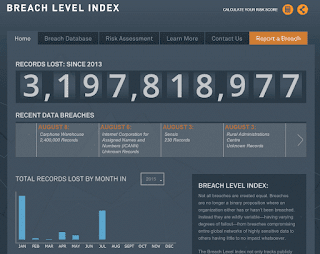
Singapore – September 9, 2015 – Gemalto (Euronext NL0000400653 GTO), the world leader in digital security, today released the findings of the Breach Level Index for the first six months of 2015, revealing that 888 data breaches occurred, compromising 246 million records worldwide.
Compared to the first half of 2014, data breaches increased by 10% while the number of compromised data records declined by 41% during the first six months of this year. This decline in compromised records can most likely be attributed to that fact that fewer large scale mega breaches have occurred in the retail industry compared to the same period last year.
Despite the decrease in the number of compromised records, large data breaches continued to expose massive amounts of personal information and identities. The largest breach in the first half of 2015 – which scored a 10 in terms of severity on the Breach Level Index – was an identity theft attack on Anthem Insurance that exposed 78.8 million records, representing almost a third (32%) of the total data records stolen in the first six months of 2015. Other notable breaches during this analysis period included a 21-million-record breach at the U.S. Office of Personnel Management (BLI: 9.7); a 50-million-record breach at Turkey’s General Directorate of Population and Citizenship Affairs (BLI: 9.3); and a 20-million-record breach at Russia’s Topface (BLI: 9.2). In fact, the top 10 breaches accounted for 81.4% of all compromised records.
“What we’re continuing to see is a large ROI for hackers with sophisticated attacks that expose massive amounts of data records. Cyber criminals are still getting away with big and very valuable data sets. For instance, the average healthcare data breach in the first half of 2015 netted more than 450,000 data records, which is an increase of 200 percent compared to the same time last year,” said Jason Hart, Vice President and Chief Technology Officer for Data Protection at Gemalto.
Data Breaches by Source
The number of state-sponsored attacks accounted for just 2% of data breach incidents, but the number of records compromised as a result of those attacks totalled 41% of all records exposed, due to the breaches at Anthem Insurance and the U.S. Office of Personnel Management. While none of the top 10 breaches from first half of 2014 were caused by state-sponsored attacks, three of the top ten this year were state sponsored—including the top two.
At the same time, malicious outsiders were the leading source of data breaches in the first half of 2015, accounting for 546 or 62% of breaches, compared to 465 or 58% in the first half of last year. Forty-six percent or 116 million of the total compromised records were attributable to malicious outsiders, down from 71.8% or 298 million in 2014.
Data Breaches by Type
Identity theft remained the primary type of breach, accounting for 75% of all records compromised and slightly more than half (53%) of data breaches in the first half of 2015. Five of the top ten breaches, including the top three – which were all classified as Catastrophic on the BLI – were identity theft breaches, down from seven of the top 10 from the same period last year.
Data Breaches by Industry
Across industries, the government and healthcare sectors accounted for about two-thirds of compromised data records (31% and 34% respectively), though healthcare only accounted for 21% of breaches this year, down from 29% compared to the same period last year. The retail sector saw a significant drop in the number of stolen data records, accounting for 4% compared to 38% for the same period last year. Across regions, the U.S. represented the largest share with three-quarters (76%) of data breaches and nearly half of all compromised records (49%). Turkey accounted for 26% of compromised records, with its massive GDPCA breach in which 50 million records were breached by a malicious outsider.
The level of encryption used to protect exposed data — which can dramatically reduce the impact of data breaches – increased slightly to 4% of all breaches compared with 1% in H1 2014.
“While the number of data breaches fluctuates, it’s still clear that breaches are not a matter of ‘if’ but ‘when.’ The Breach Level Index data shows that most companies are not able to protect their data once their perimeter defences are compromised. Although more companies are encrypting data, they are not doing it at the levels needed to reduce the magnitude of these attacks,” added Hart. “What is needed is a data-centric view of digital threats starting with better identity and access control techniques including multi-factor authentication and strong encryption to render sensitive information useless to thieves.”
According to Forrester, as cybercriminals have become more skillful and sophisticated, they have eroded the effectiveness of traditional perimeter-based security controls. The constantly mutating threat landscape requires new defensive measures, one of which is the pervasive use of data encryption technologies. In the future, organizations will encrypt data — both in motion and at rest — by default. This data-centric approach to security is a much more effective way to keep up with determined cybercriminals. By encrypting, and thereby devaluing, sensitive data, organizations can make cybercriminals bypass their networks and look for less robustly protected targets. Encryption will become a strategic cornerstone for security and risk executives responsible for their organization’s data security and privacy efforts.1
For a full summary of data breach incidents for the first half of 2015 by industry, source, type and geographic region, download the 1H 2015 Breach Level Index Report.
The Breach Level Index provides a centralized, global database of data breaches and calculates their severity based on multiple dimensions, including the type of data and the number of records stolen, the source of the breach, and whether or not the data was encrypted. By assigning a severity score to each breach, the BLI provides a comparative list of breaches, distinguishing nuisances from truly impactful mega breaches. Information populating the BLI database is based on publicly-available breach disclosure information. For more information, visitwww.breachlevelindex.com.
For the LATEST tech updates,
FOLLOW us on our Twitter
LIKE us on our FaceBook
SUBSCRIBE to us on our YouTube Channel!